Control the Sprawl of Shadow IT
Discover, assess, and control Shadow IT by automatically identifying every unsanctioned application, integration, and account in use across the enterprise. Gain clear visibility into exposure, enforce policies, remove unsafe connections, and govern SaaS usage, all without disrupting productivity.

See It. Control It. Secure It.

Control SaaS Sprawl
Discover every sanctioned and unsanctioned application in use across the enterprise, map application connections and users, analyze risk, and enable policy enforcement.

SaaS Risk Management
Continuously monitor and identify unauthorized usage, excessive permissions, and risky misconfigurations, prioritize, and remediate risks before they lead to exposure.

Threat Detection and Response
Real-time identity-centric threat analysis that correlates identity activity, permissions, and anomalies to quickly identify compromised accounts and malicious behavior.
Unseen Access Paths
The Risk
When employees adopt unsanctioned applications or connect tools without IT oversight, and integrate them with core business systems through APIs, OAuth tokens, or shared credentials, they create hidden connections that bypass security controls, and may give external services or unknown parties access to sensitive data, expanding the organization’s attack surface beyond visibility.
The Solution
Wing automatically discovers every connected application, integration, and account, including those added without IT approval. By mapping OAuth connections, API integrations, and shared credentials, Wing reveals hidden access paths, evaluates their risk and data exposure, and enables teams to enforce policies, remove unsafe connections, and restore visibility and control across the organization.
Key Features
Wing Security Platform

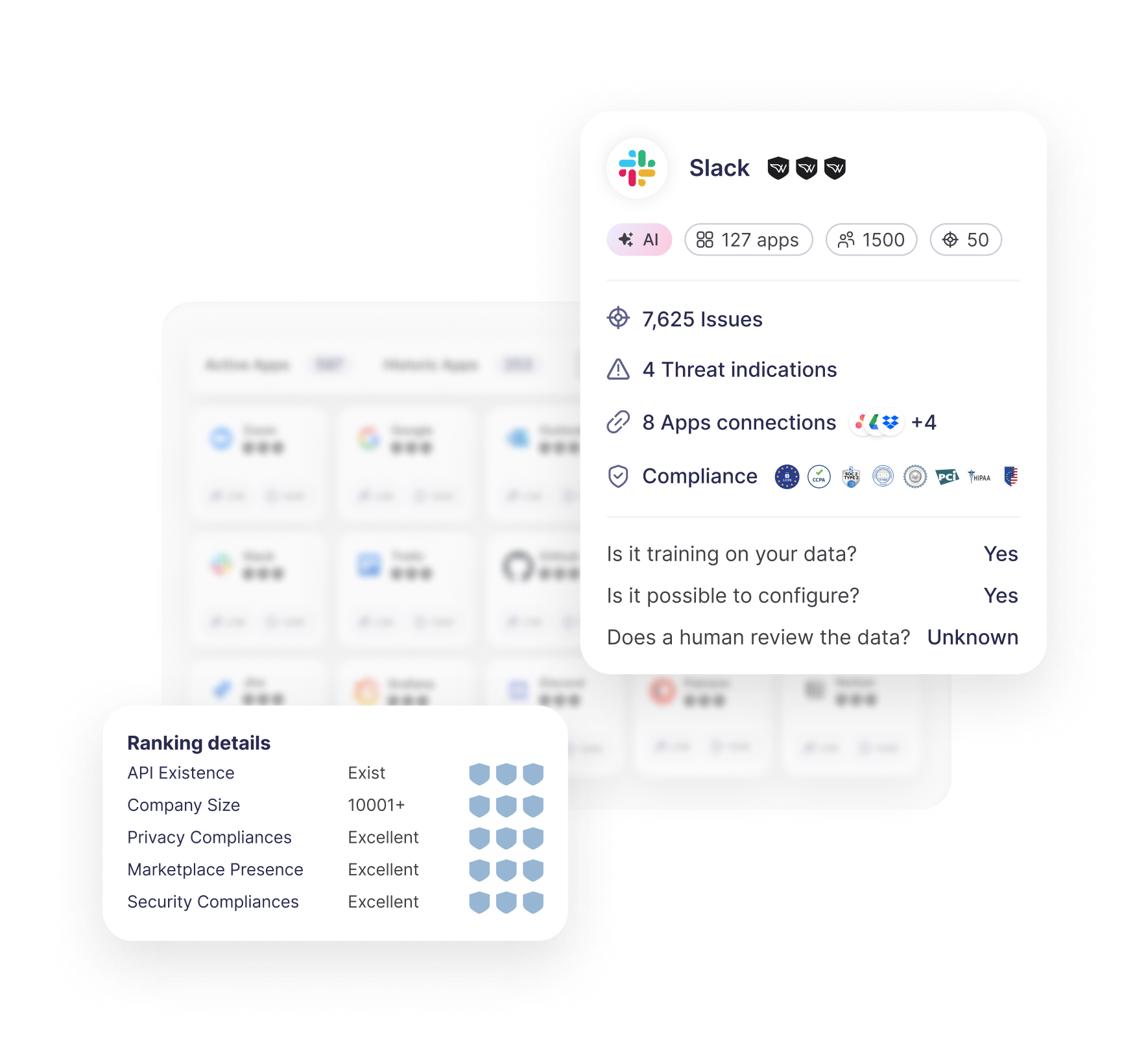
Comprehensive SaaS Discovery and Enrichment
Automatically identify every connected app and enrich it with contextual insights from the industry’s most extensive SaaS catalog, including each app’s provider, purpose, and history for informed decision-making.

SaaS Risk Assessment and Prioritization
Continuously analyse SaaS applications and integrations to evaluate misconfigurations, misuse and exposure, highlighting the issues that put your organization at risk.


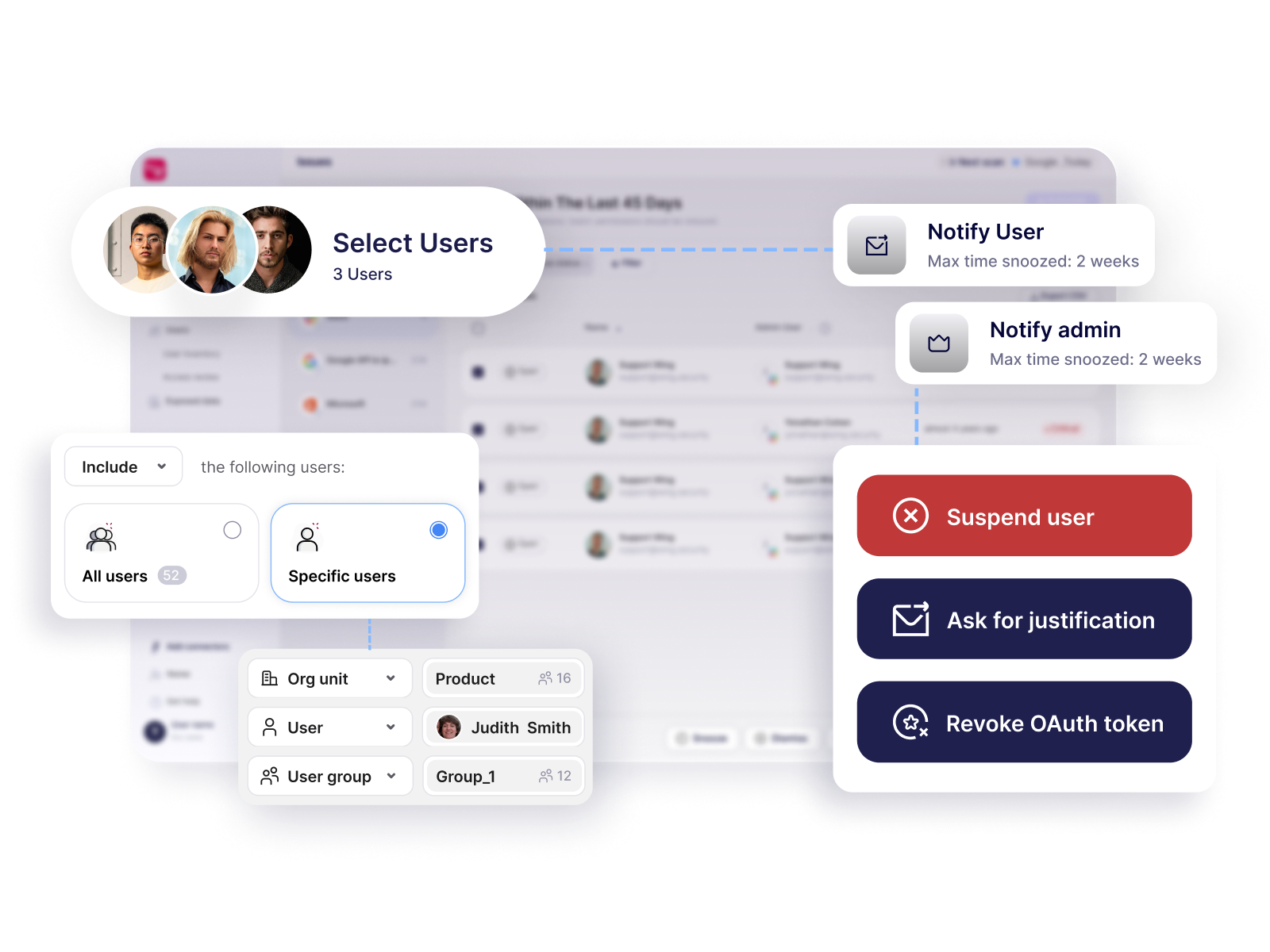
Real-Time Threat Detection and Response
Continuously monitor user and application activity to identify behavior anomalies, unauthorized access, and emerging risks, enabling instant, automated remediation.


Talk with a Wing Security expert
Let’s have a quick chat and show you Wing in action.