AI agents make you fly. Wing makes the flight safe.
Get total visibility and control over your AI agents before risk becomes a breach.

Leading organizations choose Wing.
















AI agents are the new identity gap.
Most enterprises have no clear inventory of their AI agents, no mapping of their permissions, and no visibility into how they actually behave across the stack.
AI agents break the traditional security model. They operate autonomously, often bypassing authorization boundaries.
When agents are over permissioned, unmonitored, or shared, a single prompt can lead to a cross-platform breach.
Wing’s AI agent security platform has 3 layers of visibility and remediation
Step 1: Deep Discovery of all AI usage across your stack – from tools to features to agents – all compiled in your AI inventory.
Step 2: Behavior Analysis of every identity accessing your systems, monitoring permissions, access, and cross-app actions.
Step 3: Instant Remediation to detect and respond immediately to suspicious behavior or over-permissioned agents.

Deep Discovery
Behavior Analysis
Instant Remediation

Talk with a Wing Security expert
Let’s have a quick chat and show you Wing in action.

Everything you need for agent security. In one solution.
- Deep Agent Visibility: Integrates with Microsoft Copilot, Claude, n8n, Tray.io, Glean, and more so you see what agents can access and how they operate.
- Risky Agent Behavior Detection: Uses Identity Behavior Analysis (IBA) to surface suspicious behavior like privilege escalation, access patterns, or unexpected actions.
- Connection Mapping: Detects the third-party platforms, apps, and integrations each agent can access, so you can uncover hidden exposure and reduce blind spots.
- Automated Threat Response: Revoke API keys and tokens from one place to quickly contain risky or unauthorized agent activity before it turns into an incident.
How Wing Works
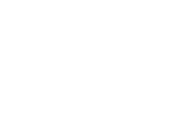
Agent Discovery
Centralized inventory via native integrations.
A continuously updated inventory of AI agent in your environment. We connect natively to agent factories, IdPs, SaaS, and cloud platforms to map ownership, origin, and access permissions.
Because agents don’t sit still: they’re created, modified, and granted permissions constantly. Live inventory is critical so that every decision is based on what’s actually happening, not outdated or incomplete data.


Agent Access Control
Managing granular permissions for identified agents.
Take control of how AI agent accesses your environment. Define and enforce granular permissions across your IdP, SaaS stack and cloud to limit what agents can reach.
So a single over-permissioned agent doesn’t turn into a full-scale breach.


Agent Threat Detection
Continuous behavioral analysis.
Monitor how an AI agent actually behaves, not just what it was supposed to do. We analyze activity against the original prompt to surface logic deviations and unauthorized privilege escalation.
So threats are stopped early, before they spread across your environment.

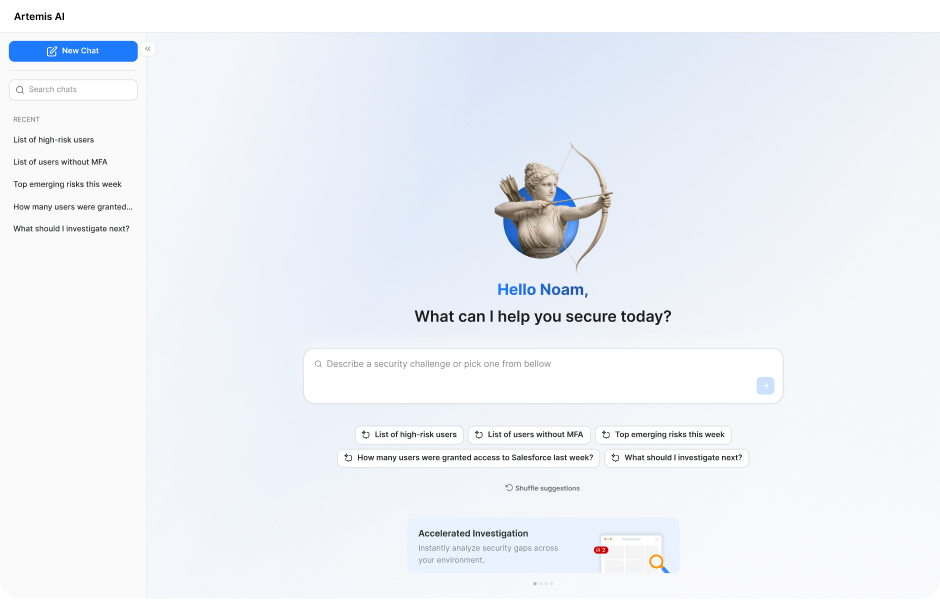
Artemis AI
The engine of intelligent AI protection.
Artemis is a specialized security agent that ingests and correlates multi-source telemetry into actionable insights for your team. It serves as our core detection brain, utilizing advanced agentic reasoning to hunt for threats and neutralize risks.
It tells your team exactly what’s happening, why it matters, and what to do next, so risks are contained fast, without slowing the business.

Resources

Talk with a Wing Security expert
Let’s have a quick chat and show you Wing in action.