Shadow IT Risk Management

Eliminate Blind Spots

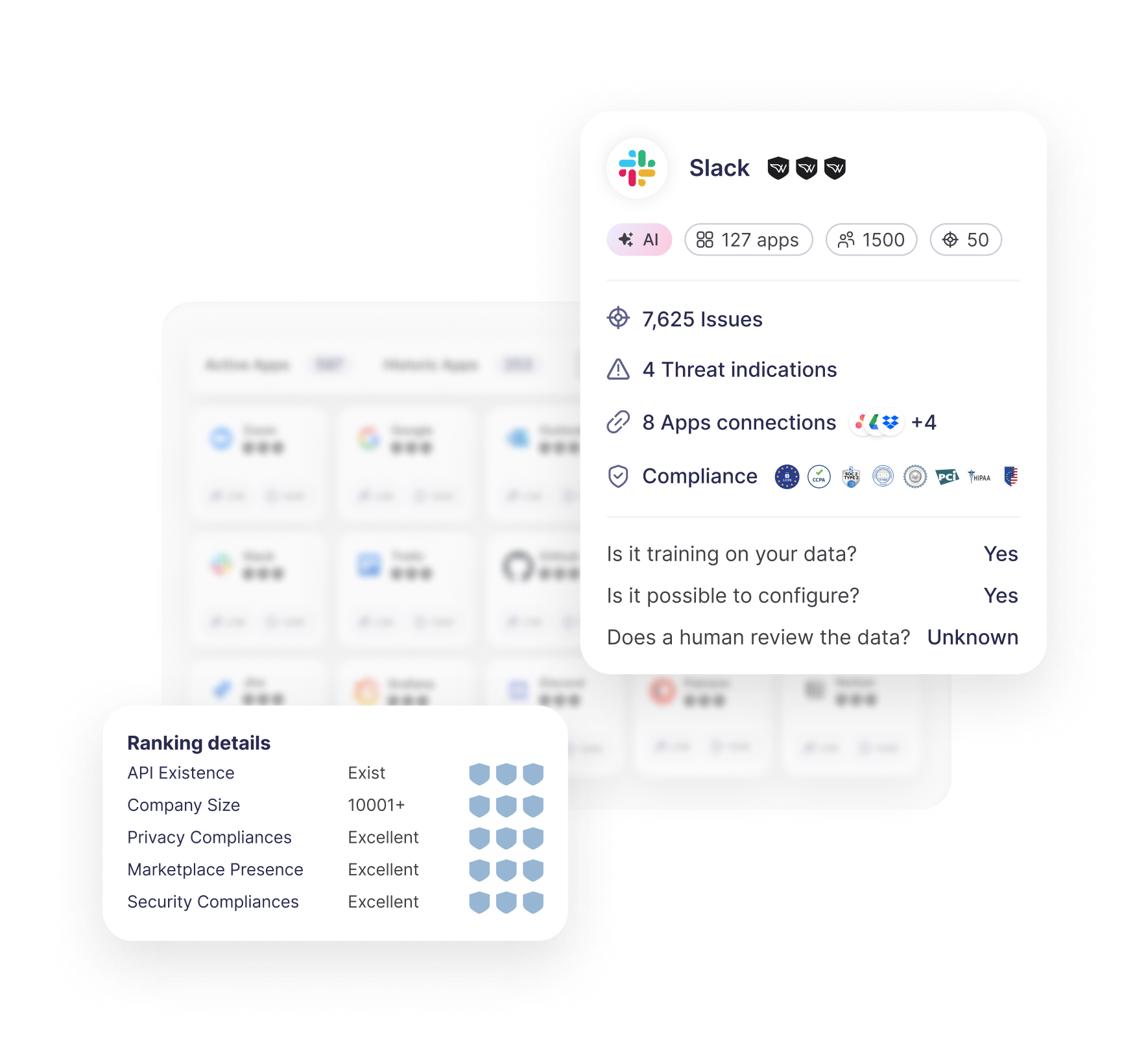
SaaS Visibility
Discover all SaaS apps (sanctioned or not) and receive contextual insights into access levels and vendor security for effective risk mitigation.

Context & Prioritization
Evaluate your SaaS ecosystem, its compliance standards, app supply chain connectivity, data handling, AI practices, and past security breaches.

Remediation & Control
Unseen Access Points
Shadow IT
The unauthorized use of SaaS applications by employees without the knowledge or approval of the IT or security teams. These apps, although often essential for employees and business operations, bypass basic security protocols and pose significant risks to your organization.
SaaS Sprawl
SaaS sprawl happens when the number of SaaS applications in use by employees grows uncontrollably, leading to increased complexity and difficulty for IT and security teams in managing SaaS security, permissions, and orphaned applications.
Key Features
Wing Security Platform

Comprehensive App Discovery and Visibility

Real-Time Risk Assessment and Prioritization


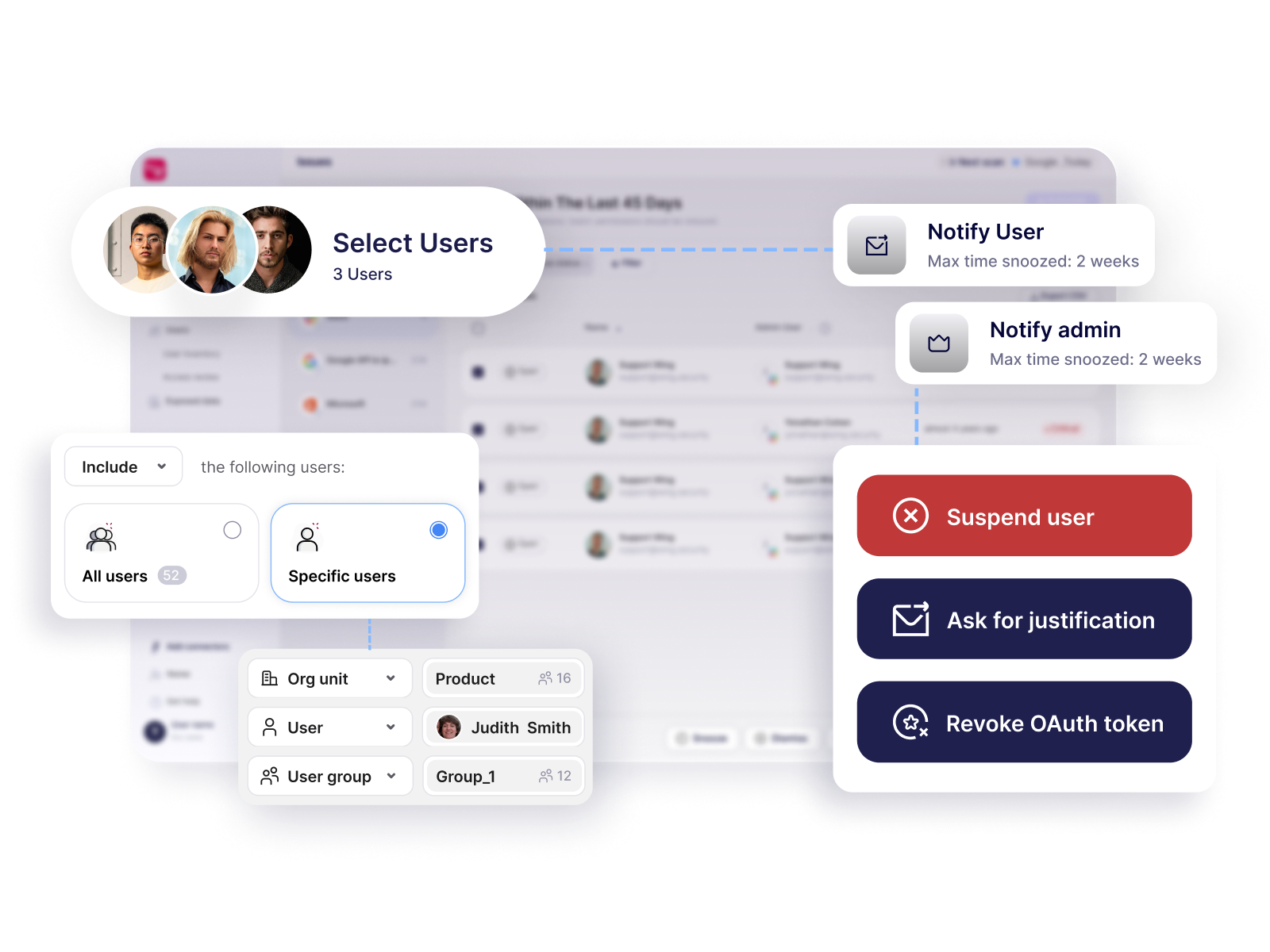
Automated Remediation and Control


Talk with a Wing Security expert
Let’s have a quick chat and show you Wing in action.

Why It Matters
Expanded Attack Surface
Every unsanctioned SaaS app adds new weaknesses to the organization’s security posture, increases the attack surface, and exposes sensitive data to cyber threats. These apps are often not monitored, allowing attackers to exploit them as weak access points, potentially leading to security breaches.
Data Compliance Violations
Shadow IT and SaaS sprawl often lead to the loss of visibility and control over where sensitive data is stored, accessed, or shared. This makes it difficult for security teams to ensure compliance with regulations like GDPR, CCPA, SOC 2, and ISO 27001. Unapproved apps may not meet the required security standards, resulting in costly fines and reputational damage.
Operational Inefficiency
SaaS sprawl creates inefficiencies and redundancies, with teams using overlapping apps for the same functions. This lack of coordination creates operational inefficiencies, drives up costs, and hampers collaboration, as data is scattered across multiple apps that aren’t integrated into the company’s IT structure.