It’s not uncommon these days to read the news, receive an email, or browse the internet and come across another AI-relate tool. The rate at which new SaaS-based AI technologies are being introduced into the market is astounding, thanks to the clear value they provide right from the start of their onboarding. Today, the use of AI tools has been a non-stop talking point to both the general public and more specifically, business professionals who are looking to gain an edge. Employees using AI tools benefit significantly from the quick answers and mostly accurate results that these tools provide, helping them do their jobs better. In this blog, we aim to address some of the key discussion points related to AI and SaaS cybersecurity.
How popular are AI applications?
To look at a single example, OpenAI’s viral chatbot, ChatGPT, has roughly 100 million users worldwide, while other generative AI tools, such as DALL·E and Bard, are also highly popular for their ability to generate impressive content – with just the click of a button. Currently, the Generative AI market is worth $13.7B and it is believed that by 2025, the generative AI market is expected to surpass $22B.
According to a GitHub DevSecOps report, in 2023, 62% of developers reported using AI/ML to check code, up from 51% in 2022. This increase is not surprising, considering that DevSecOps seek better security, more efficient DevOps practices, easier automation, cost and time-saving, and improved collaboration.
Moreover, it’s not just employees who are interested in AI. A recent Deloitte report on AI transformation revealed that 94% of business leaders believe AI is critical to organizational success in the next five years. The same report highlighted that 86% of survey respondents cited that AI enhances their performance and job satisfaction.
AI concerns and SaaS security
While the benefits of AI tools are apparent, the concerns of security professionals in organizations across the world cannot be ignored. Their basic concerns include ‘Who is using AI applications and why?’ and ‘Which AI applications exist in the organization, and what permissions have they been granted?’
Adding to these, security professionals are also concerned about data privacy and confidentiality, especially when employees may be entering sensitive company information into third-party SaaS applications like ChatGPT.
As these SaaS applications grow in popularity, so do the associated risks. Threat actors see AI applications as prime opportunities for breaching organizations, given their increasing popularity and high adoption rates. For example, ChatGPT reached one million users in just five days. To put that into perspective, it took Netflix 3.5 years to reach the same number.
But what can security teams do to protect their organizations from threat actors with malicious intentions? Especially those threat actors that are creating fake and malicious applications to trick employees and hack into their organization.
AI tools and SaaS security
The more applications in a business’s SaaS environment, the larger the attack surface and breach potential. To address this, security professionals must be aware of the increasing demand and interest in AI tools within their organizations. They should ask themselves what they can do to ensure safer SaaS usage.
Discovering and identifying which AI applications are being used within your SaaS ecosystem is the initial step in securing your organization from potential threats. As a starting point, security professionals should ask themselves two basic questions: “How many AI applications are being used within my organization?” “What permissions have those applications have been granted?”
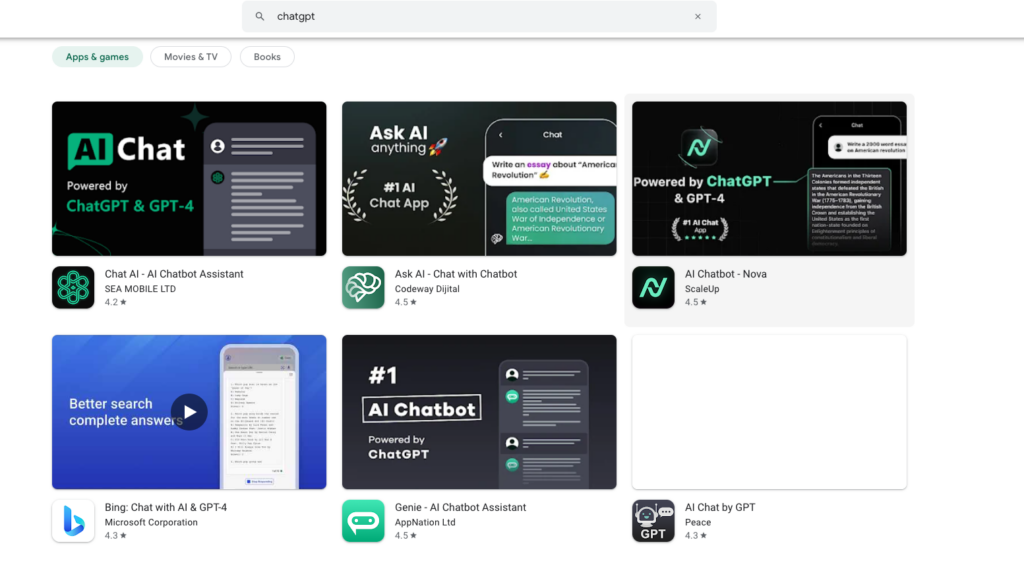
While these questions may seem super trivial at first, not knowing the answers can have severe consequences for the organization. For instance, if you are aware that employees are using AI tools like ChatGPT, do you know how many of them have accidentally used the fake versions, thinking they were downloading the legitimate application? And what permissions did they grant that application?
This innocent mistake can have far-reaching consequences. By logging in to a SaaS application using their company credentials, for example, through a Google account, they expose both themselves and the company to the opportunity for malicious software to infiltrate their SaaS application ecosystem. Once inside, the possibilities for exploiting company data become much more real.
A recent example of this was a fake, trojanized version of ChatGPT that was downloaded 9,000 times by March 2023, from a legitimate source – the Chrome Web Store. Hackers gained control of victims’ Facebook accounts, changing passwords, profile information, and disseminating false information.
Can you imagine if sensitive company information was accessed through a breach like this? The ramifications would still be felt, even today.
SaaS security solutions and AI
Moving forward, AI adoption will only increase. Therefore, it is essential for security professionals to stay on top of AI SaaS usage and have full visibility into all their organization’s SaaS applications, the users of such applications and the data connected to those applications.
Following this discovery stage – security professionals need the ability to take immediate action and remediate should they encounter any issues. However, managing such a process at an enterprise scale hasn’t always been easy. Thanks to today’s SSPM solutions that offer advanced automation, security professionals can now regain control over their SaaS issues in a much easier, faster and more effective way.
Wing has consistently demonstrated that automatic remediation is not just a nice-to-have but a non-negotiable solution to combating shadow IT and SaaS threats. With its ability to discover all applications, users, and data in an organization’s SaaS environment, it provides full visibility over all SaaS usage. At Wing, we believe that SaaS security requires an end-to-end approach. A good starting point would be to discover your SaaS applications by using Wing’s Free SaaS discovery Solution.
